Unveiling Truths Behind The Cybersecurity Profession
As news of cyberattacks and threats on organisations and governments continue to make the headlines, the demand for cybersecurity talent is rising sharply. But how does one clinch a job in the field? And what exactly is expected of a cybersecurity professional?

Tok Yee Ching spends his late nights keeping up to date with the latest happenings on cyberspace. As news of cyberattacks and threats on organisations and governments continue to make the headlines, the demand for cybersecurity talent is rising sharply. But how does one clinch a job in the field? And what exactly is expected of a cybersecurity professional?
Step into the shoes of Tok Yee Ching. The SIM-University of London Computing and Information Systems graduate spends his late nights keeping up to date with the latest trends and threats on cyberspace to counter them. While currently a PhD student at the Singapore University of Technology and Design, Yee Ching has spent a number of years delving in a wide variety of information security work and hopes to continue working and teaching in the field. At the recent ‘The Cybersecurity Awards', Yee Ching was among the 12 recipients that were recognised for their contributions in raising Singapore's standing in cybersecurity.
How did you first get into cybersecurity?
I started wondering about cybersecurity after encountering computer viruses on my family computer when I was much younger. Since then, I have always been quite intrigued by what causes computers to act up.
What was a typical day like for you as a cybersecurity professional?
My work day starts at around 7.30am where I get to office early to plan my schedule or author/review reports while having my breakfast. After this, I would be doing fieldwork such as penetration testing of systems or meeting clients to discuss findings. Alternatively, I could sometimes be also doing digital forensics work.
After the normal work day ends, I would head over to Singapore Polytechnic for my adjunct lecturing sessions from 7 to 10pm. When I'm not teaching, I would either be researching on cybersecurity or studying it to further hone my skillsets. I would also spend some time volunteering for the information security industry.
Do you really need to have a passion to work in cybersecurity?
I find that loving an area of cybersecurity has helped me immensely when I am faced with challenges- be it academically or professionally. I have quite a few examples of this. I recall when I was trying to reverse engineer a complicated piece of malware for hours where one wrong move would entail me repeating the whole process again. And on a separate occasion, I was faced with repeated failures as I attempted to find vulnerabilities in a device while the deadline was looming. I was overjoyed when I was finally able to discover the vulnerabilities. These examples make me believe that you need to love what you do.
Is a degree sufficient to enter the profession?
It really depends how you would like to chart your career path and whether you would like to enter the industry immediately. Obtaining a diploma or degree does not signify the end of learning. Attack techniques continually evolve, new methods of bypassing security mechanisms continue to be found and countermeasures are constantly developed to address such security risks. As such, it is vital for anyone considering to join the cybersecurity profession to understand that learning never stops.
How do I find the right cybersecurity domain to get into?
It takes time to find a domain that one will be truly interested in. As a student, one might find it harder to identify that domain, especially with little to no background knowledge. Being more proactive helps. They should read widely on information security, try new things out, and attend talks or events (be it free or paid). In addition, the field of information security is ever-changing and cross-domain knowledge could be an added advantage at work. There are multiple different domains and roles available (illustrated below). Red teams are professionals who focus on attack-based work, blue teams are professionals who focus on defensive or auditing-based work, and last but not least, purple teams are professionals who know both attack and defensive work.
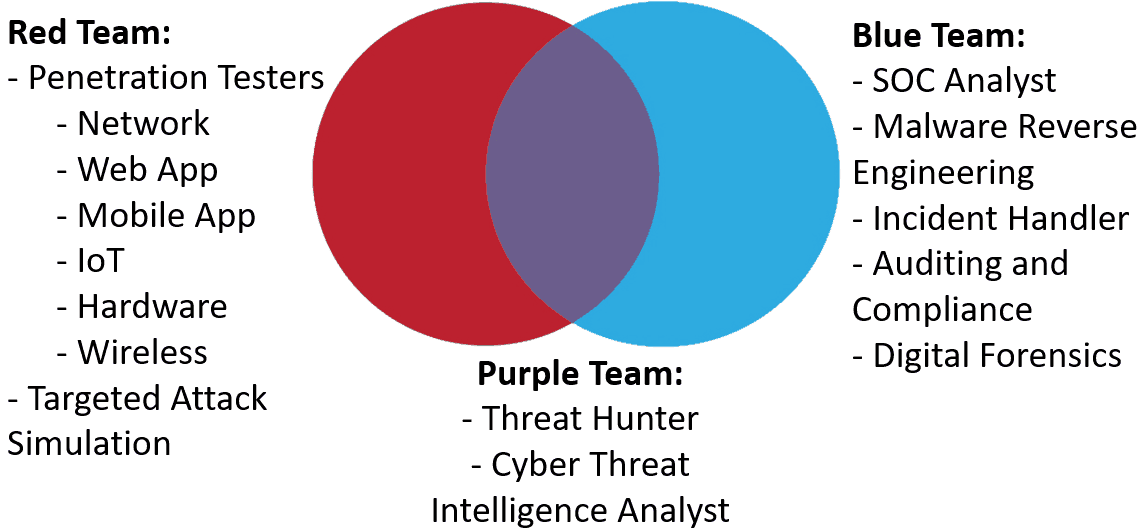
© Tok Yee Ching, 2019
What would your advice be for a university student who is looking to get a job in the cybersecurity field?
For students who are worried about not getting enough work experience, they could consider volunteering their time in cybersecurity initiatives that are looking for volunteers. Volunteering is also a journey of self-discovery, especially for individuals who are new to the cybersecurity community and industry. You might find your path in cybersecurity by being involved in interests groups such as the SIM IT Club. I discovered my interest when I was part of the SIM IT Club back in 2011 when I was working on brokering a Memorandum of Understanding (MOU) signing between SIM GE and the Association of Information Security Professionals (AISP) to set up the AiSP Student Chapter.
What do you think is the toughest challenge of being in this profession?
I would say the toughest part is making sure that my skills are being honed continuously and having to keep up with the latest developments in cybersecurity. Honing skills can cost a lot at times as one has to renew their professional training/certifications. However, it is essential to keep up to speed with the developments in cybersecurity.
What do you enjoy most about working in the cybersecurity industry?
I like that I can make a difference in strengthening the security posture of my clients or helping them regain normalcy after an incident. I am also consistently challenged to put the theory or skills that I have learnt to practice. Hence, I have a feedback mechanism where I can find out whether I truly understand something or if I require further work to get a better understanding of it.
Take your passion for cybersecurity to the next level like Yee Ching. Find out more about SIM's IT and Computer Science programmes here.
